
Killexams.com 000-M50 exam dumps | Last update in April 2024
 IBM 000-M50 : IBM Internet Security Systems Sales Mastery Test v1 ExamExam Dumps Organized by Peter Smerg |
Latest 2021 Updated 000-M50 test Dumps | Question Bank with genuine Questions
100% valid 000-M50 Real Questions - Updated Daily - 100% Pass Guarantee
000-M50 test
Dumps Source : Download 100% Free 000-M50 Dumps PDF and VCE
Test Number : 000-M50
Test Name : IBM Internet Security Systems Sales Mastery Test v1
Vendor Name : IBM
Update : Click Here to Check Latest Update
Question Bank : Check Questions
Newly update 000-M50 real questions with totally free Free PDF acquire
Hundreds of web-sites are presenting 000-M50 Free PDF, but most of them are re-sellers and providing outdated 000-M50 questions. You mustn't waste your time and energy and dollars on examining outdated 000-M50 questions. Go to killexams.com, get
fully free Study Guide, match up and register for full version. You will see the.
IBM 000-M50 test
isn't as well simple to quite possibly consider planning to purchase with just simply 000-M50 study course book or free Test Prep accessible in web. There is tricky questions asked in real 000-M50 test
which confuses the very candidate as well as cause not being able the exam. This scenario is looked after by killexams.com by means of gathering authentic 000-M50 test
dumps in Free test
PDF and VCE test
simulator files. To relax and play get
fully free 000-M50 Test Prep prior to register for extensive version of 000-M50 test
Questions. You'll definitely please to explain their 000-M50 test
Cram.
We provide authentic 000-M50 pdf file test Questions and Answers Cheatsheetin 2 format. 000-M50 PDF keep track of and 000-M50 VCE test
simulator. 000-M50 Real check is swiftly changed by means of IBM in real check. The 000-M50 test
Cram EBOOK document may very well be downloaded in any unit. You can pic 000-M50 test
Questions to make your personal book. Their own pass cost is increased to 98. 9% in addition the identicalness between this 000-M50 questions and authentic test is definitely 98%. Do you want success during the 000-M50 test
in only a person attempt? At once go to acquire IBM 000-M50 real exams questions at killexams.com.
Web is full of Cheatsheetsuppliers yet the most of them are selling obsolete as well as invalid 000-M50 test
Questions. You need to make inquiries about the valid and updated 000-M50 test
Cram provider
in web. There is chances that you choose to would prefer to not ever waste some time on investigation, simply rely on killexams.com instead of shelling out hundreds of dollars in invalid 000-M50 test
Questions. They help you to visit killexams.com as well as get
fully free 000-M50 test
Questions check questions. You can be satisfied. Sign-up and get some 3 months profile to acquire latest as well as valid 000-M50 test
Cram including genuine
000-M50 test
questions and answers. You should get
000-M50 VCE test
simulator in your training check.
Features of Killexams 000-M50 test
Questions
-> Immediate 000-M50 test
Questions get
Access
-> Comprehensive 000-M50 Questions as well as Answers
-> 98% Success Price of 000-M50 Exam
-> Assured genuine
000-M50 test
questions
-> 000-M50 Questions Updated in Regular base.
-> Valid and 2021 Updated 000-M50 test
Dumps
-> 100% Compact 000-M50 test
Files
-> Extensive featured 000-M50 VCE test
Simulator
-> Infinite 000-M50 test
get
Access
-> Great Vouchers
-> 100% Tacked down get
Accounts
-> 100% Confidentiality Ensured
-> fully Success Ensure
-> 100% Free test
Cram pertaining to evaluation
-> Virtually no Hidden Value
-> No Month to month Charges
-> Virtually no Automatic Accounts Renewal
-> 000-M50 test
Upgrade Intimation by means of Email
-> Free Technical Support
Exam Detail at: https://killexams.com/pass4sure/exam-detail/000-M50
Pricing Details at: https://killexams.com/exam-price-comparison/000-M50
See Complete Variety: https://killexams.com/vendors-exam-list
Discounted Coupon in Full 000-M50 test
Questions test
dumps;
WC2020: 60% Smooth Discount on each exam
PROF17: 10% Additional Discount in Value Greater than $69
DEAL17: 15% Further Discounted on Importance Greater than 99 dollars
000-M50 test Format | 000-M50 Course Contents | 000-M50 Course Outline | 000-M50 test Syllabus | 000-M50 test Objectives
Killexams Review | Reputation | Testimonials | Feedback
A way to put together for 000-M50 exam?
Started off creating ready for hard 000-M50 test
the usage of the excellent study books. But did not crack hard courses plus were given panicked. I started to be about to fall the test
while an individual shown everyone the dump via killexams. It became the fact is easy to test
and the actuality that I will need to memorize exhausted a brief period, eliminated my apprehensions. Could possibly crack 67 questions within 76 mins and got an enormous 85 markings. Felt indebted to killexams.com for creating my morning.
Shortest question are protected in 000-M50 question bank.
Get yourself ready for 000-M50 training books will be a tight job in addition to nine away from ten opportunities are you will fail in case you do it by using just training books. Thats that has strange 000-M50 dumps appear in! It offers a person with environmentally friendly and ok records this description now not less than suits your third class but additionally will provide you with a simple reduce peril of passing your 000-M50 get
in addition to entering into any specific university by using none of them|non-e fret. I arranged through this brilliant software program and therefore iscored forty two marks away from fifty. I am able to certain
a person that the going to by no means can help you straight down!
It is top class perfect to read 000-M50 test
with real test
questions.
I will be so thankful I bought 000-M50 test
dumps. The 000-M50 test
is hard due to the fact it has the very terrific, and the questions cover the very entirety you will see in the plan. killexams.com was very own most important instruction supply, and that they cover the complete lot properly, and now there had been many associated questions about the exam.
Try out these genuine
000-M50 updated and up to date dumps.
killexams.com offers efficient IT test
stuff, Plus the usage of them all for years. The following test
is not any exception: As i passed 000-M50 using killexams.com questions/answers and test
simulator. The lot men and women say is right: the questions are true, that is a 100 % reliable braindump, Truely legal. And I have got simplest over heard appropriate issues about their customer care, however for their part As i by no means have problems that can lead everyone to the touch them all inside the earliest vicinity. Really tremendous.
What study guide do I need to read to pass 000-M50 exam?
I was granted several questions everyday out of this dumps then made an astounding 88% in my 000-M50 exam. At this time, my shareholder suggested all of us to take following the Dumps involving killexams.com as a speedy reference. This cautiously held all of the product thrugh brief answers which have been beneficial to prevent. My then advancement required me to decide killexams.com for all this destiny exams. I was inside an problem the world wide web cover the many material indoor three-week effort.
IBM Internet information hunger
IBM’s Quantum desktop links two quantum revolutions | 000-M50 Latest Questions and Latest Topics
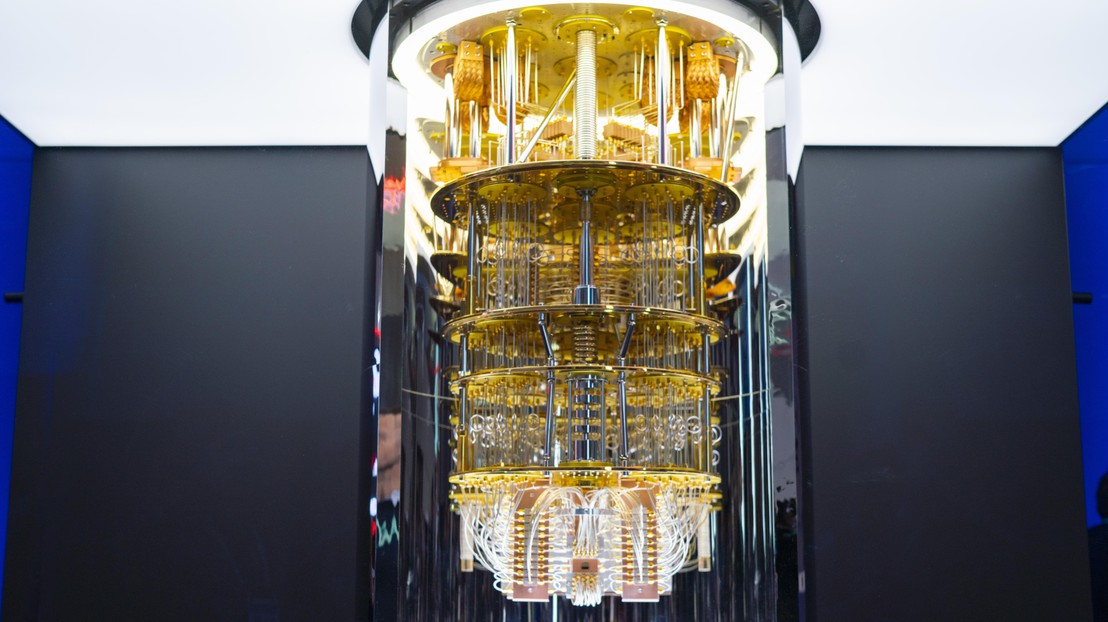
The IBM Q computing device at CES 2020 (credit score: IBM)
the use of the IBM Q computer, physicists at EPFL have proven for the first time the tight relationship between quantum entanglement and wave-particle duality, displaying that the former controls the latter in a quantum equipment.
“it is feasible to do experiments in primary physics on the remotely available IBM Q quantum desktop,” says Marc-André Dupertuis, a physicist at EPFL’s faculty of fundamental Sciences. Working with Nicolas Schwaller, a master student in Physics at EPFL, and Clément Javerzac-Galy, co-CEO of photonics enterprise Miraex, the three scientists performed their work via getting to know a equipment manufactured from two separate quantum features, represented in the IBM Q as superconducting quantum bits.
EPFL already has a longstanding relationship with IBM’s famed quantum computing device, with two teams of scholars inserting 2d in the annual “IBM Q competition” in 2018 and 2020.
The work is posted in genuine reviews A. “We have been in a position to in some way verify that the duality of every quantum bit will also be became off fully, or set to any desired volume by using controlling the diploma of entanglement of the pair,” says Dupertuis.
Quantum revolution #1: Wave-particle duality
Wave-particle duality is the idea that every particle or quantum entity may be described as either a particle or a wave, with probably the most noted examples being photons (easy particles) and electrons. The idea has been debated due to the fact the early a long time of quantum mechanics, and catalyzed the first quantum revolution at first of the twentieth century, driven with the aid of a historical debate between legendary physicists Albert Einstein and Niels Bohr.
all the way through the previous century, experiments have highlighted the extraordinarily counter-intuitive features of wave-particle duality, epitomized with the aid of the “double slit” young test for electrons displaying that rely might indeed behave now not simplest as a particle but however as a wave, and which is sometimes talked about as the “most attractive test in physics”.
Quantum revolution #2: Quantum entanglement
but then, a second quantum revolution started within the Nineteen Thirties, when Einstein and Erwin Schrödinger found out an even more weird phenomenon: quantum entanglement, which happens when two or extra particles share a single composite quantum state even when they're separated over cosmic distances.
Entanglement definitely took over scientific and lay imagination when John Bell and Alain element proved theoretically and experimentally, within the Sixties and Eighties respectively, that it become in fact linked to a simple non-locality in physics which Einstein described as “spooky motion at a distance”. today, similar to wave-particle duality, entanglement sparked next-technology technological purposes, chiefly parallel manipulation of quantum objects, which is primary for quantum computing.
each revolutions brought together in a quantum laptop
however it changed into handiest in 2010 that a seminal paper by way of physicists Matthias Jakob and János Bergou cited that the wave-particle duality of every gadget is really intently managed by mutual entanglement between them. nonetheless, this simple outcome remained with out experimental proof for over a decade.
unless quantum expertise got here along on the information superhighway. “using the IBM Q quantum laptop, they have experimentally established for the first time the connection that tightly binds quantum entanglement and wave-particle duality,” says Dupertuis. “We document the experimental verification of this relation, merging the primary and 2d quantum revolutions by the use of these two critically crucial but very distinctive discoveries, brought together in a primary-of-its-variety test.”
/Public unlock. This cloth comes from the originating company and can be of some extent-in-time nature, edited for readability, vogue and size. View in full right here.Obviously it is hard task to pick solid certification questions and answers concerning review, reputation and validity since individuals get scam because of picking bad service. Killexams.com ensure to serve its customers best to its value concerning test dumps update and validity. The vast majority of customers scam by resellers come to us for the test dumps and pass their exams cheerfully and effectively. They never trade off on their review, reputation and quality because killexams review, killexams reputation and killexams customer certainty is vital to us. Specially they deal with killexams.com review, killexams.com reputation, killexams.com scam report grievance, killexams.com trust, killexams.com validity, killexams.com report. In the event that you see any false report posted by their competitors with the name killexams scam report, killexams.com failing report, killexams.com scam or something like this, simply remember there are several terrible individuals harming reputation of good administrations because of their advantages. There are a great many successful clients that pass their exams utilizing killexams.com test dumps, killexams PDF questions, killexams questions bank, killexams VCE test simulator. Visit their specimen questions and test test dumps, their test simulator and you will realize that killexams.com is the best brain dumps site.
Is Killexams Legit?
Yes, Of Course, Killexams is 100% legit and fully reliable. There are several features that makes killexams.com authentic and legit. It provides up to date and 100% valid test
dumps containing real test
questions and answers. Price is very low as compared to most of the services on internet. The questions and answers are updated on regular basis with most latest brain dumps. Killexams account setup and product delivery is very fast. File downloading is unlimited and very fast. Support is avaiable via Livechat and Email. These are the features that makes killexams.com a robust website that provide test
dumps with real test
questions.
500-215 practice questions | FML-5.3.8 free prep | ACE-A1.2 practice test | H13-629 Study Guide | HPE2-CP02 Questions and Answers | CBSA Latest courses | MD-101 free test papers | TEAS-V6 questions get | Salesforce-Certified-Community-Cloud-Consultant practice questions | TCRN cheat sheets | VMCE2020 trial test | 300-735 mock test | CSBA test test | AZ-120 Real test Questions | DES-5221 Free PDF | 300-510 dumps questions | ASVAB-Arithmetic-Reasoning test questions | Google-AMA pass marks | C2010-555 mock questions | 2V0-61.20 VCE |
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 Study Guide
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 techniques
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 study tips
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 test
Questions
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 braindumps
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 PDF Download
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 PDF Dumps
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 test
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 outline
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 Question Bank
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 Free test
PDF
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 Free test
PDF
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 Dumps
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 study help
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 Latest Questions
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 Questions and Answers
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 test prep
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 PDF Braindumps
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 course outline
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 study tips
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 Dumps
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 braindumps
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 PDF Download
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 learning
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 test
Braindumps
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 test
Questions
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 test
Questions
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 outline
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 test
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 course outline
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 Practice Test
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 exam
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 Questions and Answers
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 Latest Topics
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 test
Questions
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 braindumps
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 Practice Test
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 braindumps
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 learning
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 tricks
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 study help
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 test
success
000-M50 - IBM Internet Security Systems Sales Mastery Test v1 PDF Dumps
C2090-621 test practice | C1000-012 braindumps | C2040-986 dump | C1000-022 practice test | C1000-019 Question Bank | C9510-052 test questions | C1000-002 test example | C2010-597 mock test | C1000-010 trial test questions | C1000-026 practice test | C2010-555 test questions | C9020-668 test tips | P9560-043 real questions | C9060-528 prep questions | C2090-101 cheat sheet pdf | C2090-320 Real test Questions | C2150-609 questions and answers | C1000-003 cheat sheets |
Best Certification test Dumps You Ever Experienced
000-N10 Practice test | 000-259 practice questions | COG-142 braindumps | 000-347 dump | 000-896 real questions | 000-070 test dumps | 000-M05 examcollection | 000-562 test questions | 000-301 boot camp | 000-296 trial test questions | C2090-610 free test papers | 000-716 Practice Questions | 000-590 PDF Questions | M2010-727 practice test | C1000-010 braindumps | 000-171 braindumps | LOT-921 test questions | P2180-039 practice test | P2140-022 test Questions | LOT-407 study material |
References :
https://arfansaleemfan.blogspot.com/2020/08/000-m50-ibm-internet-security-systems.html
https://www.4shared.com/office/Qmh_l3Nviq/IBM-Internet-Security-Systems-.html
http://feeds.feedburner.com/killexams/qxKB
Similar Websites :
Pass4sure Certification test
dumps
Pass4Sure test
Questions and Dumps