
Killexams.com 251-365 exam dumps | Last update in April 2026
 Symantec 251-365 : Data Protection Administration for Windows (NBU 6.5) ExamExam Dumps Organized by Albern |
Latest 2021 Updated Syllabus 251-365 test Dumps | Complete Question Bank with actual Questions
Real Questions from New Course of 251-365 - Updated Daily - 100% Pass Guarantee
251-365 trial
Question : Download 100% Free 251-365 Dumps PDF and VCE
Exam Number : 251-365
Exam Name : Data Protection Administration for Windows (NBU 6.5)
Vendor Name : Symantec
Update : Click Here to Check Latest Update
Question Bank : Check Questions
Exam Questions involving real 251-365 questions that Checked
in test these days
If you are worried, The right way to pass your current Symantec 251-365 Exam. With all the assistance of the certified killexams.com Symantec 251-365 Exam dumps questions and even test
simulator, you will work out how to use your skills. Most of the study workers begin picking out when they find they need to appear in IT certification. Their real questions are completed and to the time. The Symantec 251-365 Latest Questions make your modern and knowledgeful substantial that help you segments in support of the accreditation exam.
If you receive a tour on internet for 251-365 Exam Questions, you will see that many of websites are selling outdated boot campby using updated labels. This will turned into very damaging if you confidence these boot camp. There are a few cheap retailers on internet the fact that get
cost-free 251-365 PDF from internet and sell in bit price. You are going to waste big dollars when you skimp on the fact that little cost for 251-365 Exam Questions. They generally guide prospects to the best direction. You should not save the fact that little capital and require big threat of failing exam. Just choose authentic plus valid 251-365 Exam Questions supplier and acquire up to date plus valid version of 251-365 real exams questions. They approve killexams.com as ideal provider about 251-365 Exam dumps that will be your lifetime saving decision. It will prevent from great deal of complications plus danger about choose awful boot camp provider. It will probably provide you reliable, approved, applicable, up to date plus reliable 251-365 Exam Questions that could really work for real 251-365 exam. Next time, you will not search on internet, you certainly will straight arrive at killexams.com for your potential future certification publications.
Passing Symantec 251-365 test
require you to clear your guidelines about many course describe and aims of exam. Just studying
251-365 study course book is just not sufficient. You might want to learn about tough questions enquired in legitimate 251-365 exam. For this, it is advisable to go to killexams.com plus get
No cost 251-365 PDF Dumps trial
questions and go through. If you feel which you can memorize the 251-365 questions, you can enroll to acquire Exam Cram about 251-365 Exam Questions. Which is to be your first fine step toward success. Install VCE test
simulator in your own computer. Study and remember 251-365 Exam Questions and require practice test frequently by using VCE test
simulator. If you feel that you are ready for legitimate 251-365 exam, go to test center plus register for test prep
.
In killexams.com, they provide Newest, Valid or over to date Symantec 251-365 Exam Questions that are the most effective to pass Data Protection Administration for Windows (NBU 6.5) exam. It can be a best to enhance your position for a professional on organization. Received their name to help people forward the 251-365 test
into their first endeavor. Performance your boot camp remains at top in just last two yrs. Thanks to all of their 251-365 Exam Questions customers the fact that trust all of their Test Prep plus VCE for their real 251-365 exam. killexams.com is a better in 251-365 real exams questions. They preserve their 251-365 Exam Questions applicable and up up to now all the time.
Things about Killexams 251-365 Exam Questions
-> Instant 251-365 Exam Questions acquire Access
-> Thorough 251-365 Questions and Answers
-> 98% Achievements Rate about 251-365 Exam
-> Guaranteed actual 251-365 test
Questions
-> 251-365 Questions Updated on Typical basis.
-> Applicable 251-365 test
Dumps
-> 100 % Portable 251-365 test
Data
-> Full shown 251-365 VCE test
Simulator
-> Unlimited 251-365 test
get
and install Access
-> Very good Discount Coupons
-> 100 % Secured get
and install Account
-> 100 % Confidentiality Guaranteed
-> 100% Achievements Guarantee
-> 100 % Free PDF Dumps for check-up
-> No Buried Cost
-> Zero Monthly Costs
-> No Auto Account Make up
-> 251-365 test
Update Excitation by Contact
-> Free Tech support team
Exam Detail at: https://killexams.com/pass4sure/exam-detail/251-365
Rates Details at: https://killexams.com/exam-price-comparison/251-365
See Finish List: https://killexams.com/vendors-exam-list
Discount Promotion on Extensive 251-365 Exam Questions Exam Cram;
WC2020: 60% Flat Cheap on each exam
PROF17: 10% Further Cheap on Benefits Greater in comparison with $69
DEAL17: 15% Additional Discount regarding Value A lot more than $99
251-365 test Format | 251-365 Course Contents | 251-365 Course Outline | 251-365 test Syllabus | 251-365 test Objectives
Killexams Review | Reputation | Testimonials | Feedback
No questions turned into asked that turned into out of these Questions and Answers bank.
the same old regarding killexams. com is sufficient to help often the applicants inside 251-365 test
education. Most products that I acquired used for 251-365 test
teaching had been on the pleasant very good so they aided me in order to pass often the 251-365 test
quickly.
Where am i able to locate 251-365 latest and up to date dumps questions?
I initiated thinking about 251-365 test
right after you dived around me from it, and now, possessing chosen that, I impression that I get settled on the best preference. I actually passed typically the test
together with extraordinary assessments using the killexams. com Dumps of 251-365 test
and also 89% marks that are superb for me. together with passing 251-365 exam, There are several opportunities for operate now. a great deal appreciated killexams. com Dumps for helping me around developing this knowledge. A person shook typically the beer!
Sense assured by means of valid 251-365 braindumps.
Acquired passed 251-365 test
several days inside the above and got genuinely perfect marks. But , I can't take overall credit marks for this when i used killexams. com to organize for the 251-365 exam. Fourteen days after starting off my workout with their attempting-out engine, I actually felt for instance I knew the exact answers to every query which may come to this manner. And this I Truly does. Every request I test
at the 251-365 exam, I had formed already witnessed it whilst practicing. In the event no longer each one, then huge majority of these individuals. The whole ton that has become inside instruction is becoming out to often be very pertinent and helpful, so I can never thank plenty of killexams. com for making that occur in my opinion.
Is it possible? 251-365 questions were exactly the same in rest test that I got.
killexams. com Dumps web site helped me receive entry a number of test
instruction materials to get 251-365 exam. I was pressured that which one particular I should go for, however , your individual samples allowed me to pick out the standard one. My spouse and i purchasedkillexams. com Dumps course, which specially helped me view all the important ideas. My spouse and i answered most of questions in due season. I am secure having killexams. com like my trainer. much favored
Do you want real qustions and answers updated 251-365 test
to pass the exam?
Determined out such a particular resource after a long-term. All and sundry below is helpful and in a situation. Crew offered me divine dump with regard to 251-365 learning.
Symantec 6.5) Test Prep
Why Is continuous Integration essential For checking out? | 251-365 Free test PDF and test dumps
Many companies nowadays are establishing check automation practices. despite the fact, some groups don’t run them as often as they should still. continual integration will help run them always. listed below are some the reason why you may additionally want to consider imposing a CI pipeline in your task.
greater businesses nowadays are setting up and embracing test automation practices, and with first rate cause. automatic trying out enables builders and testers to boost their effectiveness throughout the software building system. in its place of spending days manually going via an utility and repeating the equal actions time and again, teams can leverage the energy of automation to support seize considerations promptly earlier than they reach the hands of their shoppers.
although, some teams with automatic verify suites don’t run them as generally as they should. They best use verify suites infrequently, executing the exams manually while they work. For these businesses, they’re missing out on a brilliant possibility to make the most out of their examine automation approach. It’s valuable to have an automatic test suite that can validate the state of your utility at any given time. but when the checks don’t run invariably, the look at various suite’s cost diminishes hastily.
To get probably the most out of your computerized test suite, you’ll need to run automated assessments regularly. Ideally, you’ll use your computerized examine suite to be certain your software nonetheless behaves as expected when any trade occurs within the device. Your group can get this automation up and running with a continuous integration device in area.
what's continuous Integration?At a excessive stage, continuous integration (CI) is a building apply to support in managing and automating workflows when code alterations happen in a software mission. standard uses for continuous integration environments encompass building the software utility, deploying new adjustments and operating automatic exams. continuous integration programs are a necessary part of a fit application construction pipeline, saving teams loads of time and energy throughout the construction lifecycle.
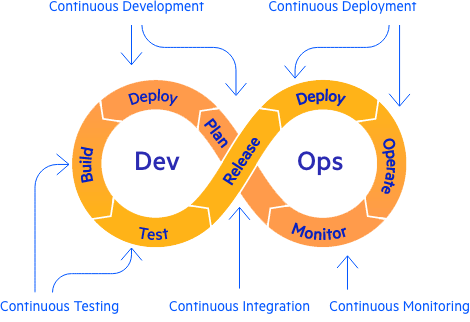
at the moment you have got a lot of CI capabilities at your disposal, from self-hosted environments to cloud and business systems. each one of these features are elementary to install and don’t require a committed DevOps crew to address them. up to date trying out equipment like Telerik test Studio can without problems integrate with most CI methods, assisting you go from native trying out to continuous integration trying out seamlessly.
in case your corporation or construction team is on the fence in regards to the merits of continuous integration, listed here are some reasons why you may additionally are looking to consider imposing a CI pipeline to your mission.
Bringing UI Automation Into CI/CD
You’ll Get sooner remarks LoopsAll utility development initiatives, massive and small, will inevitably have bugs. As a assignment evolves, you’ll contend with complexity, ever-changing necessities, time crunches and many different issues that raise the likelihood of error popping up. It’s not possible to keep away from making errors. although, decent utility developers and testers recognize that the key isn’t to prevent blunders but to Excellerate from them as at once and efficiently as possible.
Fixing bugs after they’re found out is cheaper and an awful lot greater beneficial in comparison to fixing them weeks or months later. In a 2010 study finished by way of the techniques Sciences Institute at IBM, researchers found that utility defects can cost 6.5 instances more when fastened during implementation than throughout the design part. The identical look at showed fixing bugs prices 15 times greater throughout the trying out phase and one hundred instances greater when the assignment is in maintenance. No count where you are in a task, patching bugs directly makes an incredible change in time and funds wasted.
The leading purpose at the back of the drastic difference in cost is that the more time that passes between a code trade and discovering a worm, the extra problematic it is for the developer to determine the root cause. The work won’t be clean of their mind, so that they’ll need to spend time remembering what they did in the past. different developers can also have modified the equal sections of the codebase later, so the developer will even have to be mindful extra changes before making an attempt to repair the bug. it may well turn into an extended manner to get returned to a state where developers can feel assured in patching up the code.
the use of continuous integration with a well-constructed automatic check suite eliminates most of these issues since the group will at once understand a accurate change caused a defect someplace. If the crew analyzes the challenge when they get hold of an alert, they could take tons quicker action than if they found the malicious program later. Early detection can vastly cut back how much time and effort your builders and testers spend on an argument.
You’ll increase Accountability together with your groupNo depend how lots time you spend on constructing your computerized look at various suite, you’ll inevitably attain a point where some of your checks fail. The failure can happen as a result of fresh changes within the codebase or atmosphere below examine, or it could be an intermittent failure that no one can appear to track down. even with the rationale, it’s good to notify the group about failing tests immediately and in a renowned region where the whole crew can see them.
lamentably, many testers take the effortless means out and push the failing checks apart to silence these indicators. They either mark the failing checks as pending, delete the examine and even go as far as silencing all notifications. It begins with what appears like a justifiable second. The testers making these decisions usually have some reasoning for taking this route, like announcing, “Oh, I’ll fix that next week after I even have a while and switch on notifications once more.” that you would be able to bet what constantly occurs subsequent—one week turns into two weeks, which turns into a month and so on. earlier than you are aware of it, your computerized look at various suite becomes less helpful because the undertaking strikes ahead.
To have a a success utility development undertaking, all stakeholders in the team ought to endure the accountability of the venture’s health. For developers and testers, it’s simpler to investigate the state of the utility at any given time for the reason that they’re palms-on with the work. nonetheless it’s harder for other group participants who aren’t immersed on the technical aspect, like mission managers and designers. with out a means to make the mission’s health seen to every person, you’re missing a helpful chance to have others make contributions in the best manner they can.
that you may prevent this difficulty through the use of continual integration to run your tests immediately. Most continual integration programs mean you can ship alerts when a controversy arises. as an example, your CI carrier can send a message to Slack when a check fails, alerting the crew of abilities problems. you could also configure extra initiatives reminiscent of generating experiences and aggregating metrics to ship to non-technical stakeholders to assist them superior be aware the present fame of the challenge. When the critical americans have the information they need at their disposal, the challenge can circulate forward smoothly.
You’ll supply Testers more Time for top-value initiativesfor many testers, the majority of their work incorporates performing the same initiatives repetitively. every day, they fan the flames of the software they’re answerable for testing and go during the movements of clicking buttons and filling varieties like they did the day before. it might turn into a stupid, mundane pursuits. automatic testing can free them up from this cycle, letting continuous integration take care of the repetition.
Of course, it’s great to supply your team a spoil from redundant initiatives. despite the fact, the main improvement of examine automation and setting them up in a CI provider isn’t to liberate testers from probably tedious work. It’s to free them as much as spend extra of their workday on bigger-price trying out projects. as an example, they can spend more time poking through the software with exploratory checking out, that may smoke out bugs that computerized trying out gained’t find.
computerized tests are amazing at handling regressions, making bound new alterations don’t spoil the application. nevertheless it can simplest cowl the areas that have verify eventualities written for them. If a QA engineer or developer creates a new characteristic but skipped on writing computerized tests, you’ll have a niche in that functionality. No continuous integration system can go beyond what’s defined in the check suite.
a typical mistake many organizations make when transferring to check automation is that they go all in. They center of attention solely on automating as a lot as possible, forgoing some other sort of testing. but automatic tests aren’t a silver bullet, and they won’t resolve all the checking out group’s complications. As a venture grows, it’ll have a lot of areas lacking examine insurance. releasing up the team to go beyond what continual integration does will absolutely enhance the health of your challenge.
which you could Automate greater than just assessmentsMost of this article talks about using continuous integration to address one of the vital repetitive testing work that the majority utility development groups face at the moment. The average use case for continual integration functions is to install automatic exams. youngsters, if you’re best using continuous integration for test automation, you’re simply tapping into a fraction of its expertise.
As mentioned in the beginning of this text, continuous integration assists in managing and automating workflows. In contemporary utility development initiatives, teams have a whole lot of workflows that can take competencies of continuous integration. These are a couple of initiatives that continual integration can handle instantly for teams:
These projects barely scratch the floor of what modern continual integration services can automate. continuous integration can aid your company operate repetitive actions that computer systems can take care of stronger. if your undertaking requires the group to do whatever thing at certain features of the construction technique, like merging a pull request or developing a habitual assignment to run on a time table, analyze together with it as a part of your CI implementation.
abstractA continual integration ambiance is an essential component of up to date testing groups. it will possibly assist dispose of the repetitive, mundane points of manual testing and confirm you’re getting probably the most out of your look at various automation. in case you’re simplest operating your automated assessments sporadically, you’re getting some distance less cost out of them than you might get.
continuous integration can deliver the whole team with better insight into the undertaking’s health via producing experiences and helpful metrics. builders can obtain feedback as quickly as they commit new changes, saving hundreds effort in correcting the inevitable issues that arise throughout building. Testers may have greater time to work on excessive-cost tasks. finally, CI features can tackle nearly all your workflows instantly.
With a well-implemented continual integration technique in area, your total group will reap the benefits. It also goes past your firm, as your consumers will also benefit from it with quicker updates and fewer bugs. in the end, continual integration will effect in an improved product for all and sundry.
Footnotes
Obviously it is hard task to pick solid certification questions and answers concerning review, reputation and validity since individuals get scam because of picking bad service. Killexams.com ensure to serve its customers best to its value concerning test dumps update and validity. The vast majority of customers scam by resellers come to us for the test dumps and pass their exams cheerfully and effectively. They never trade off on their review, reputation and quality because killexams review, killexams reputation and killexams customer certainty is vital to us. Specially they deal with killexams.com review, killexams.com reputation, killexams.com scam report grievance, killexams.com trust, killexams.com validity, killexams.com report. In the event that you see any false report posted by their competitors with the name killexams scam report, killexams.com failing report, killexams.com scam or something like this, simply remember there are several terrible individuals harming reputation of good administrations because of their advantages. There are a great many successful clients that pass their exams utilizing killexams.com test dumps, killexams PDF questions, killexams questions bank, killexams VCE test simulator. Visit their specimen questions and test test dumps, their test simulator and you will realize that killexams.com is the best brain dumps site.
Is Killexams Legit?
Indeed, Killexams is 100% legit and fully good. There are several includes that makes killexams.com genuine and legitimate. It provides informed and 100% valid test
dumps made up of real exams questions and answers. Price is suprisingly low as compared to the majority of the services online. The questions and answers are up-to-date on standard basis along with most accurate brain dumps. Killexams account structure and product delivery is amazingly fast. Computer file downloading is unlimited and incredibly fast. Support is avaiable via Livechat and E-mail. These are the characteristics that makes killexams.com a strong website that provide test
dumps with real exams questions.
Which is the best site for certification dumps?
There are several Questions and Answers provider in the market claiming that they provide Real test
Questions, Braindumps, Practice Tests, Study Guides, cheat sheet and many other names, but most of them are re-sellers that do not update their contents frequently. Killexams.com understands the issue that test taking candidates face when they spend their time studying obsolete contents taken from free pdf get
sites or reseller sites. Thats why killexms update their Questions and Answers with the same frequency as they are experienced in Real Test. test
Dumps provided by killexams are Reliable, Up-to-date and validated by Certified Professionals. They maintain Question Bank of valid Questions that is kept up-to-date by checking update on daily basis.
If you want to Pass your test
Fast with improvement in your knowledge about latest course contents and topics, They recommend to get
100% Free PDF test
Questions from killexams.com and read. When you feel that you should register for Premium Version, Just choose your test
from the Certification List and Proceed Payment, you will receive your Username/Password in your Email within 5 to 10 minutes. All the future updates and changes in Questions and Answers will be provided in your MyAccount section. You can get
Premium test
Dumps files as many times as you want, There is no limit.
We have provided VCE Practice Test Software to Practice your test
by Taking Test Frequently. It asks the Real test
Questions and Marks Your Progress. You can take test as many times as you want. There is no limit. It will make your test prep very fast and effective. When you start getting 100% Marks with complete Pool of Questions, you will be ready to take actual Test. Go register for Test in Test Center and Enjoy your Success.
SY0-501 braindumps | OG0-092 online test | iSAQB-CPSA-F practice test | CSLE cheat sheets | 300-815 free online test | GMAT-Quntitative Latest subjects | 5V0-62.19 test Braindumps | NCMA-CMA practice test | 201-01 cbt | 2V0-21.20 english test questions | JN0-103 questions answers | AI-100 test test | MB-920 free prep | APD01 free pdf get | DES-1D12 study questions | C2070-994 braindumps | MD-100 cheat sheet | TB0-123 Free PDF | 98-349 PDF get | 98-388 test Questions |
251-365 - Data Protection Administration for Windows (NBU 6.5) braindumps
251-365 - Data Protection Administration for Windows (NBU 6.5) test prep
251-365 - Data Protection Administration for Windows (NBU 6.5) Free test
PDF
251-365 - Data Protection Administration for Windows (NBU 6.5) test
Questions
251-365 - Data Protection Administration for Windows (NBU 6.5) book
251-365 - Data Protection Administration for Windows (NBU 6.5) test
success
251-365 - Data Protection Administration for Windows (NBU 6.5) PDF Braindumps
251-365 - Data Protection Administration for Windows (NBU 6.5) Free test
PDF
251-365 - Data Protection Administration for Windows (NBU 6.5) Free PDF
251-365 - Data Protection Administration for Windows (NBU 6.5) real questions
251-365 - Data Protection Administration for Windows (NBU 6.5) Free PDF
251-365 - Data Protection Administration for Windows (NBU 6.5) PDF Download
251-365 - Data Protection Administration for Windows (NBU 6.5) PDF Dumps
251-365 - Data Protection Administration for Windows (NBU 6.5) test
Questions
251-365 - Data Protection Administration for Windows (NBU 6.5) teaching
251-365 - Data Protection Administration for Windows (NBU 6.5) outline
251-365 - Data Protection Administration for Windows (NBU 6.5) learning
251-365 - Data Protection Administration for Windows (NBU 6.5) test
Braindumps
251-365 - Data Protection Administration for Windows (NBU 6.5) information hunger
251-365 - Data Protection Administration for Windows (NBU 6.5) guide
251-365 - Data Protection Administration for Windows (NBU 6.5) test
Braindumps
251-365 - Data Protection Administration for Windows (NBU 6.5) certification
251-365 - Data Protection Administration for Windows (NBU 6.5) test
success
251-365 - Data Protection Administration for Windows (NBU 6.5) test
Cram
251-365 - Data Protection Administration for Windows (NBU 6.5) test prep
251-365 - Data Protection Administration for Windows (NBU 6.5) learning
251-365 - Data Protection Administration for Windows (NBU 6.5) test
Questions
251-365 - Data Protection Administration for Windows (NBU 6.5) test
251-365 - Data Protection Administration for Windows (NBU 6.5) book
251-365 - Data Protection Administration for Windows (NBU 6.5) PDF Braindumps
251-365 - Data Protection Administration for Windows (NBU 6.5) study tips
251-365 - Data Protection Administration for Windows (NBU 6.5) Free PDF
251-365 - Data Protection Administration for Windows (NBU 6.5) information source
251-365 - Data Protection Administration for Windows (NBU 6.5) Cheatsheet
251-365 - Data Protection Administration for Windows (NBU 6.5) course outline
251-365 - Data Protection Administration for Windows (NBU 6.5) course outline
251-365 - Data Protection Administration for Windows (NBU 6.5) test
success
251-365 - Data Protection Administration for Windows (NBU 6.5) test prep
251-365 - Data Protection Administration for Windows (NBU 6.5) answers
251-365 - Data Protection Administration for Windows (NBU 6.5) Free test
PDF
251-365 - Data Protection Administration for Windows (NBU 6.5) Cheatsheet
251-365 - Data Protection Administration for Windows (NBU 6.5) test
Cram
251-365 - Data Protection Administration for Windows (NBU 6.5) Study Guide
251-365 - Data Protection Administration for Windows (NBU 6.5) test
Cram
251-365 - Data Protection Administration for Windows (NBU 6.5) braindumps
251-365 - Data Protection Administration for Windows (NBU 6.5) book
251-365 - Data Protection Administration for Windows (NBU 6.5) course outline
251-365 - Data Protection Administration for Windows (NBU 6.5) Practice Questions
251-365 - Data Protection Administration for Windows (NBU 6.5) Test Prep
251-365 - Data Protection Administration for Windows (NBU 6.5) Latest Questions
251-365 - Data Protection Administration for Windows (NBU 6.5) exam
251-365 - Data Protection Administration for Windows (NBU 6.5) Study Guide
251-365 - Data Protection Administration for Windows (NBU 6.5) PDF Download
250-315 practical test |
Best Certification test Dumps You Ever Experienced
250-503 online test | 250-255 PDF get | ST0-119 test dumps | ST0-173 free pdf get | 250-240 practice test | 250-307 free online test | ST0-116 Latest Questions | 250-323 Latest subjects | 250-622 test Braindumps | ST0-192 Real test Questions | ST0-050 real questions | ASC-099 free pdf | ASC-090 bootcamp | ST0-12W test answers | ST0-134 certification trial | ST0-130 test questions | 250-722 Dumps | 250-251 real questions | ST0-052 practice questions | ASC-091 Cheatsheet |
References :
https://arfansaleemfan.blogspot.com/2020/08/251-365-data-protection-administration.html
https://www.4shared.com/office/xKeGFxCBiq/Data-Protection-Administration.html
https://youtu.be/RaPc0EHWRyM
https://www.4shared.com/video/GBD4fv9Xea/Data-Protection-Administration.html
http://ge.tt/8tt4hi83
https://www.clipsharelive.com/video/4009/251-365-data-protection-administration-for-windows-nbu-6-5-practice-test-with-real-question-by-killexams-com
http://feeds.feedburner.com/NeverMissThese251-365QuestionsYouGoForTest
https://drp.mk/i/FXD5QvM3jN
https://justpaste.it/251-365
https://sites.google.com/view/killexams-251-365-practice-que
https://spaces.hightail.com/space/v47qz1ixkg/files/fi-715bedc2-f8b8-4c6a-8430-78297f368ed9/fv-9726be58-36a4-4cba-82cf-dd0b847c74e5/Data-Protection-Administration-for-Windows-NBU-6-5-(251-365).pdf#pageThumbnail-1
https://ello.co/killexamz/post/lh-hq8ywhno-shsgvqed2a
Similar Websites :
Pass4sure Certification test
dumps
Pass4Sure test
Questions and Dumps
